In the landscape of modern business technology, a phenomenon known as "Shadow IT" has emerged as a critical area of focus. Since the inception of remote, and more recently, hybrid working styles, shadow IT has been on the rise.
Shadow IT refers to the use of IT systems, software, and services within an organisation without explicit approval from the IT department. This includes everything from cloud services and external applications to personal devices used for work purposes.
Shadow IT is a double-edged sword. It empowers employees to find creative solutions and tools that increase productivity and efficiency, often bypassing the traditional, sometimes slower, channels of IT approval. However, it introduces significant risks, including security vulnerabilities, data breaches, and compliance issues. These tools and applications are not under the direct oversight of the organisation's IT governance structures.
Understanding Shadow IT is crucial for modern businesses. It's a growing trend; with the rise of easily accessible cloud-based services and the increasing sophistication of consumer technology, employees are more likely than ever to seek out their own solutions. Managing Shadow IT is not about outright prohibition but finding a balance between flexibility and control. Businesses need to develop strategies to harness the innovative potential of Shadow IT while mitigating its risks. This requires a deep understanding of why employees turn to these solutions and how they can be integrated safely and effectively into the company's IT ecosystem.
Shadow IT is a reflection of the changing dynamics in the workplace, where traditional boundaries between personal and professional technology use are increasingly blurred. Businesses that seek to stay ahead must not only recognise the existence of Shadow IT but actively engage with it, crafting policies and practices that address its challenges while capitalising on its many potential benefits.
What is Shadow IT?
Shadow IT refers to the use of information technology systems, devices, software, applications, and services within an organisation without formal approval from the IT department, and often, without their knowledge entirely. This concept has evolved significantly over the years, paralleling the rapid advancements in technology and the changing landscape of the workplace.
Shadow IT emerged from the gaps between an organisation's IT provisions and the actual needs or preferences of its employees.
In the early days, it might have been as simple as an employee using a personal data storage device to transfer files for convenience. However, with the advent of cloud computing and the proliferation of SaaS (Software as a Service) applications, Shadow IT has grown both in complexity and scale.
Today, it encompasses a wide range of technologies and services, often cloud-based, that employees adopt to meet their immediate needs without waiting for official IT approval.
The evolution of Shadow IT reflects a fundamental shift in how technology is consumed and managed in the workplace. It's driven by the desire for greater agility, efficiency, and user satisfaction. Employees, seeking to avoid the perceived red tape and delays of official IT channels, often find quicker, more user-friendly solutions independently. This trend has been further accelerated by the consumerisation of IT, where the lines between personal and professional technology use are closer than ever before.
Common Forms of Shadow IT in the Workplace
Shadow IT can take many forms in the workplace, some of the most common being:
- Cloud Storage and File Sharing Services: Applications like Dropbox, Google Drive, and OneDrive are popular for their convenience and ease of use, allowing employees to store, share, and access files from anywhere. However, they can pose significant data security risks if used without proper oversight. Once an employee begins this practice, it's easy to begin mishandling commercially sensitive data that can lead to large-scale risks for the business.
- Communication and Collaboration Tools: Tools such as Slack, Zoom, and Skype, often adopted for team collaboration and communication, can bypass official channels. While they enhance productivity, they can also lead to data leaks if not properly managed.
- Personal Devices (BYOD): The Bring Your Own Device (BYOD) trend, where employees use their personal smartphones, tablets, or laptops for work, is a significant aspect of Shadow IT. These devices often escape the security parameters set by the organisation, potentially exposing sensitive information.
- Unsanctioned Software and Applications: Employees may download and use software that offers more features or is more user-friendly than approved alternatives. This includes everything from productivity tools, project management software, to specialised software for specific job functions.
- Custom Scripts and Solutions: In some cases, employees or departments develop custom scripts, macros, or even full-fledged applications to automate tasks or solve specific problems, often without IT's knowledge or support.
Understanding these common forms of Shadow IT is the first step in managing them effectively. It's about recognising the reasons behind their adoption and addressing the underlying needs they fulfil, all while ensuring that the organisation's security and compliance requirements are not compromised.
What Leads To Shadow IT?
The primary motivators driving employees towards Shadow IT are efficiency, productivity, and the lack of speed within internal IT teams. In many cases, the official IT solutions provided by organisations do not align perfectly with the specific needs or preferences of individual employees or teams. This misalignment often results in employees seeking out alternative technologies that they perceive as more efficient or better suited to their tasks. We also often hear that employees get tired of waiting for weeks, months, and sometimes even years, to see progress on their organisation implementing new or improved IT solutions.
- Speed and Ease of Use: Many Shadow IT tools offer a more user-friendly experience and can be quickly implemented without the lengthy approval processes associated with official IT channels. Employees often find these tools more intuitive and better designed to meet their immediate needs.
- Filling the Gaps: In some instances, the existing IT infrastructure may lack certain functionalities or be outdated. Employees turn to Shadow IT to fill these gaps, using tools that offer the specific features they need to perform their jobs more effectively.
- Collaboration and Accessibility: With the rise of remote work and global teams, employees often seek tools that offer better collaboration features and accessibility across different devices and locations, something that traditional IT solutions may not always provide.
Real-world Examples of Shadow IT Usage
Marketing Team Using Unsanctioned Analytics Tools
A marketing team in a mid-sized company started using an advanced, cloud-based analytics tool that was not approved by their IT department. The tool offered real-time data analysis and insights that were not available in the company's officially sanctioned software, leading to more effective marketing campaigns and a significant increase in ROI. Sounds good, right?
The analytics tool, though, did not adhere to the same stringent data security and privacy standards that the company's approved systems did. This posed a risk of sensitive marketing data, possibly including customer information, sales figures, and commercial website data being exposed to potential breaches or unauthorised access.
It's not just the regulatory risks that arise with this form of misuse, however. The use of the unsanctioned tool created isolated data silos within the organisation. This meant that critical data insights and information generated by the tool were not accessible company-wide, leading to a fragmented view of marketing strategies and customer data.
Sales Department Adopting a New CRM System
In a large enterprise, the sales department found the officially provided CRM system cumbersome and not tailored to their specific workflow. They adopted a more agile, cloud-based CRM tool, which allowed them to track customer interactions more effectively and resulted in increased sales and better customer relationship management. What a great result, you're thinking...
What the sales department didn't know, was that the data was being held in a US-based data centre that was transferring and storing data in a way that didn't comply with the EU GDPR regulations that their organisation was bound by. By utilising the unauthorised tool they had placed their organisation's data in risk of non-compliance with data protection laws. The financial penalties of which can be £17.5 million, or up to 4% of global turnover, whichever is higher. Enough to take most businesses out of action forever.
These real-world examples illustrate the ways in which Shadow IT can manifest in different departments of any business. They highlight the need for companies to understand the motivations behind Shadow IT usage and to find ways to integrate these tools into their official IT ecosystem safely and effectively, or alternatively, provide approved solutions that are effective for business requirements.
The Risks of Shadow IT
While shadow IT often arises from a desire to improve efficiency and productivity, unmanaged shadow IT carries with it a host of significant risks. These risks range from serious security vulnerabilities, potentially leading to data breaches, to compliance and legal challenges that can have substantial repercussions for the organisation.
Shadow IT can severely impact the governance and control mechanisms of IT departments, leading to a fragmented technology strategy and operational inefficiencies. Understanding and mitigating these risks is crucial for maintaining the integrity, security, and efficiency of an organisation's IT infrastructure.
Security Vulnerabilities and Data Breaches
One of the most significant risks associated with unmanaged Shadow IT is the increased vulnerability to security breaches. When employees use unsanctioned software, applications, or devices, these often fall outside the purview of the organisation's standard security protocols. This lack of oversight can lead to several issues:
- Weak Security Measures: Shadow IT solutions may not have robust security features, making them susceptible to cyber attacks, malware, and hacking.
- Data Leakage: There's a heightened risk of sensitive company or customer data being leaked, either accidentally or through malicious attacks, as these tools are not typically subject to the same rigorous data protection standards.
- Untracked Access Points: Each unsanctioned application or device can act as an entry point for cyber threats, increasing the organisation's attack surface.
Compliance Issues and Legal Implications
Shadow IT can also lead to serious compliance and legal issues, particularly for organisations in highly regulated industries:
- Non-Compliance with Regulations: Use of unauthorised tools may violate laws and regulations like GDPR, HIPAA, or SOX, which have strict guidelines on data handling and privacy.
- Legal Liability: If a breach occurs due to Shadow IT, the organisation could face legal action, fines, and damage to its reputation.
- Audit Failures: Unmanaged IT assets can lead to failures in audits, as there might be unaccounted for software or data processing activities.
Impact on IT Governance and Control
Unmanaged Shadow IT can significantly undermine the governance and control that IT departments have over their technological environments:
- Lack of Visibility and Control: IT departments lose visibility into what applications and tools are being used, making it difficult to manage and secure the IT environment effectively.
- Inefficient Resource Utilisation: Shadow IT can lead to duplication of IT efforts and resources, as different teams may use different tools for similar purposes without the knowledge of the IT department.
- Difficulty in Troubleshooting and Maintenance: When issues arise with Shadow IT tools, IT teams may struggle to provide support or maintenance, as they are not familiar with these systems. This can lead to prolonged downtimes and reduced productivity.
- Challenge in Strategic IT Planning: The presence of Shadow IT makes it challenging for IT leaders to plan strategically, as they do not have a complete picture of the organisation's IT landscape.
Disruption in Workflow Integration
- Inconsistent Data Syncing: Issues arise when Shadow IT does not integrate with the company's central systems, leading to data inconsistencies.
- Workflow Interruptions: Lack of integration can disrupt workflows that rely on shared information or assets.
Unaccounted Changes in IT Infrastructure
- Unforeseen Disruptions: IT updates may inadvertently disrupt Shadow IT tools, impacting their functionality.
- Network Changes Impact: Changes in network resources can unexpectedly affect the performance of Shadow IT assets.
Challenges in Network Management
- Bandwidth Consumption: Unsanctioned applications may consume excess network bandwidth.
- Network Conflicts: Shadow IT can create conflicts, reducing overall network efficiency and reliability.
While Shadow IT can arise from a genuine need for more efficient and effective tools, its unmanaged presence poses significant risks to an organisation's security, compliance posture, and overall IT governance. It is crucial for organisations to find a balance between allowing innovation and maintaining control over their IT environments.
The Benefits of Shadow IT
After everything that's been said, you wouldn't be wrong to be concerned or to believe that Shadow IT is a dark evil that must be eradicated from the world of IT. However, there are some benefits that can be weighed up against the risks we've outlined.
Innovation and Agility in the Workplace
Shadow IT, despite its risks, can be a significant driver of innovation and agility within a business. Employees often turn to unsanctioned tools and technologies to overcome limitations in the existing IT infrastructure, inadvertently fostering a culture of innovation. These tools can introduce new capabilities and efficiencies, enabling teams to respond more quickly to changing business needs and market trends. For instance, a team might use a new project management tool that offers better features than the officially sanctioned one, leading to more efficient project tracking and delivery.
Employee Empowerment and Satisfaction
The use of Shadow IT can also lead to greater employee empowerment and job satisfaction. When employees find and use tools that better suit their workflow and preferences, it can lead to a sense of ownership and autonomy in their work. This empowerment often translates into higher job satisfaction and productivity. For example, an employee might use a more intuitive data visualisation tool, enabling them to create more impactful reports and presentations, thereby enhancing their job satisfaction and output quality.
Examples of Positive Outcomes from Shadow IT
- Enhanced Collaboration: A team might start using an unauthorised communication tool that offers superior features compared to the official one, leading to improved collaboration and team dynamics.
- Rapid Problem-Solving: Employees might deploy a cloud-based tool to quickly address a business challenge, demonstrating initiative and problem-solving skills that benefit the organisation.
- Cost Savings: In some cases, Shadow IT tools can be more cost-effective than their sanctioned counterparts, offering similar or better functionality at a lower cost.
- Discovery of Innovative Solutions: Shadow IT can act as a testing ground for new technologies. When employees experiment with new tools, they can sometimes identify solutions that the IT department can later adopt officially, leading to overall technological advancement within the organisation.
- Increased Responsiveness to Customer Needs: By using more agile and customer-friendly tools, employees can often provide better service to customers, enhancing customer satisfaction and loyalty.
While it is important to manage the risks associated with Shadow IT, it's equally crucial to recognise the potential benefits it can bring in terms of innovation, employee satisfaction, and overall business agility. By understanding and harnessing these benefits, business units can create a more dynamic, responsive, and efficient work environment.
Create a Shadow IT Strategy
Balancing the risks and rewards of Shadow IT requires strategic management and a proactive approach. Here are some strategies to effectively manage these risks:
- Conducting Regular IT Audits: Regular audits can help identify the presence of Shadow IT within the business. These audits should assess the usage, security, and compliance aspects of all IT tools and systems.
- Improving Official IT Solutions: Shadow IT arises from inadequacies in the sanctioned IT infrastructure. By improving these systems and ensuring they meet employee needs, organisations can reduce the reliance on unsanctioned tools.
- Employee Education and Awareness: Educating employees about the risks associated with Shadow IT and promoting awareness of IT policies can help mitigate its use.
- Encouraging Open Communication: Creating channels for employees to express their needs and frustrations with current IT solutions can help the IT department address these issues proactively.
Developing a Policy Framework for Shadow IT
A well-defined policy framework is essential for managing Shadow IT. This framework should include:
- Clear Usage Policies: Define what is permissible and what is not. Include guidelines on the use of personal devices and third-party applications.
- Process for Tool Evaluation and Approval: Establish a streamlined process for employees to request and get approval for new tools and technologies.
- Data Security and Compliance Standards: Ensure that all tools, whether sanctioned or not, adhere to the organisation's data security and compliance standards.
- Consequences of Non-Compliance: Outline the consequences of using unauthorised tools to ensure employees understand the seriousness of bypassing IT protocols.
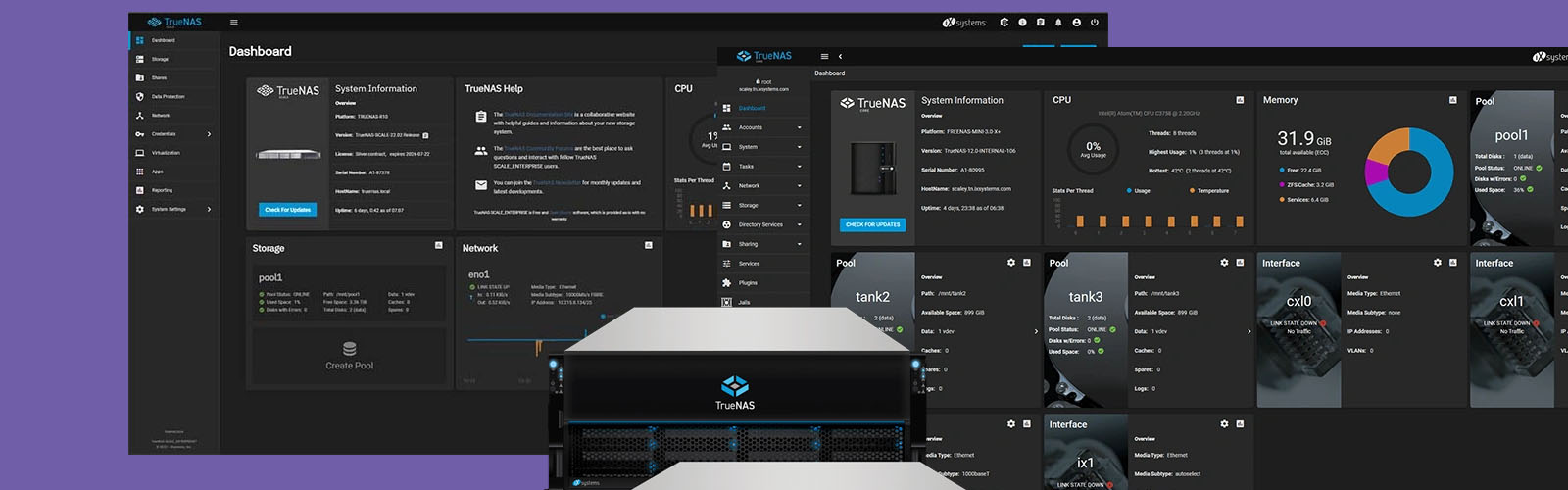
Tools and Technologies for Monitoring and Controlling Shadow IT
Leveraging the right tools and technologies is crucial for monitoring and controlling Shadow IT:
- Network Monitoring Solutions: Use network monitoring tools to detect unsanctioned devices and applications on the corporate network.
- Application Management Systems: Implement systems that can manage and control the installation and usage of software across the organisation.
- Cloud Access Security Brokers (CASBs): CASBs can help in monitoring and managing cloud applications and services, providing visibility into cloud-based Shadow IT.
- Endpoint Management Tools: These tools can help in managing and securing endpoints, ensuring that only authorised devices and applications are used for corporate purposes.
By balancing the risks and rewards of Shadow IT through effective management strategies, policy frameworks, and the use of appropriate tools, organisations can harness the benefits of employee-driven innovation while maintaining control over their IT environment and mitigating potential risks.
Predicting The Future of Shadow IT
As we look towards the future, Shadow IT is expected to continue evolving, influenced by several key trends:
- Increased Cloud Adoption: With more businesses moving to cloud-based solutions, the ease of accessing and deploying cloud services will likely lead to an increase in Shadow IT activities.
- Rise of Remote Work: The shift towards remote and hybrid work models will further blur the lines between personal and professional technology use, potentially leading to more Shadow IT scenarios.
- Greater Emphasis on User Experience: As employees become more tech-savvy, there will be a growing demand for tools that offer superior user experience. This could drive employees to seek out and use unsanctioned tools that better meet their needs.
- Advancements in Technology: Emerging technologies like AI, machine learning, and IoT will offer new tools and platforms for employees, potentially increasing the scope and complexity of Shadow IT.
Shadow IT - An Overview
Key Takeaways - What To Teach Your Organisation
Shadow IT, defined as the use of unauthorised software, applications, or devices within an organisation, presents a complex challenge in modern businesses. While it can drive innovation and employee satisfaction, it also introduces significant risks, including security vulnerabilities, compliance issues, and business inefficiencies. The key to managing Shadow IT lies in striking a balance between the need for control and flexibility.
- Security and Compliance Risks: Unmanaged Shadow IT can lead to data breaches and non-compliance with regulatory standards.
- Business Inefficiencies: It can disrupt workflows and lead to resource misallocation and network management challenges.
- Innovation and Employee Empowerment: On the positive side, Shadow IT can foster innovation and improve employee job satisfaction.
- Balancing Risks and Rewards: Effective management strategies, policy frameworks, and monitoring tools are essential for mitigating risks while harnessing the benefits of Shadow IT.
- Evolving Landscape: The future of Shadow IT is intertwined with trends like increased cloud adoption and the rise of remote work, necessitating adaptive IT management strategies.
Key Actions - What Your Organisation Should Do
For businesses, the aim is clear: proactively manage Shadow IT to harness its potential benefits while mitigating its risks. This requires a multifaceted approach:
- Develop a Comprehensive Understanding: Gain a thorough understanding of the extent and nature of Shadow IT within your organisation.
- Foster Open Communication: Encourage a culture where employees feel comfortable discussing their technology needs and challenges.
- Implement Flexible and Adaptive IT Policies: Develop IT policies that are flexible enough to accommodate new technologies and employee needs while maintaining security and compliance.
- Invest in User-Friendly Enterprise Solutions: Choose enterprise tools that match the user experience of consumer-grade solutions to reduce the allure of unauthorised tools.
- Educate and Train Employees: Regularly educate your workforce about the risks associated with Shadow IT and the importance of adhering to IT policies.
- Leverage Technology for Monitoring and Control: Utilise advanced monitoring and security tools to keep a check on unauthorised software and devices.