The Rise of the Zero Trust Cyber Security Model


In an increasingly interconnected world, cybersecurity has become a critical concern for individuals, businesses, and governments alike. Traditional cybersecurity models, such as perimeter-based security measures, have long been the go-to solution for protecting sensitive data and infrastructure. However, as the threat landscape continues to evolve, these approaches are proving less effective in the face of sophisticated cyberattacks and insider threats. This has prompted the need for a more robust and comprehensive approach to cybersecurity.
If you read our 10 predictions for cyber security in 2023, you'll have been introduced to the Zero Trust model, an innovative framework that redefines how organisations protect their data and digital assets. The Zero Trust model operates on the principle of "never trust, always verify," ensuring that every user, device, and connection within the network is authenticated and authorised before access is granted. This shift in security philosophy has garnered significant attention and adoption across various industries.
In this article, we will explore the rise of the Zero Trust cybersecurity model, delving into its key principles, the benefits it offers, and its increasing relevance in today's rapidly changing digital landscape. By examining the limitations of traditional cybersecurity models and the advantages of the Zero Trust approach, we aim to provide valuable insights for organisations considering the adoption of this progressive security framework.
The roots of cybersecurity can be traced back to the early days of computing when simple measures, such as passwords, were introduced to protect access to computer systems. As the internet and digital technology evolved, so did the threats. Hackers and cybercriminals became increasingly resourceful, exploiting vulnerabilities in systems and networks to gain unauthorised access, steal sensitive data, and disrupt operations.
In response to these growing threats, organisations began implementing perimeter-based security models. These models focused on creating a virtual "wall" around their network infrastructure to keep malicious actors out while allowing legitimate users to access the resources they needed. Key components of these models include:
While these security measures were effective for a time, the rapid evolution of technology and the increasing sophistication of cyber threats have exposed several limitations in traditional models:
Given these limitations, it has become increasingly clear that a new approach to cybersecurity is necessary—one that can address the challenges posed by modern threats and complex IT environments. This has led to the development and rise of the Zero Trust security model.
The Zero Trust model is a cybersecurity framework that shifts the focus from perimeter-based defences to a more holistic approach that assumes no user, device, or network connection can be trusted by default. In this model, every access request is thoroughly verified, regardless of its origin, before granting access to resources.
The Zero Trust model is built upon three core principles that guide its implementation:
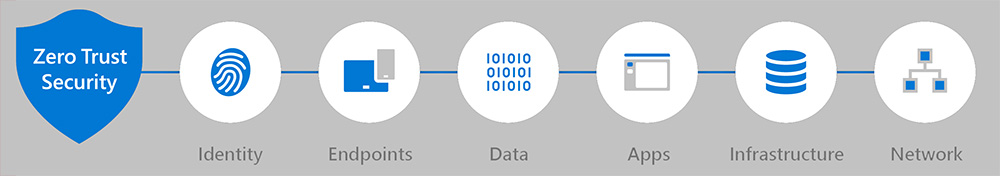
The implementation of a Zero Trust security model involves several key components that work together to ensure robust protection:
By embracing these principles and components, the Zero Trust model aims to provide organisations with a more robust and adaptive security framework, capable of addressing the complexities and challenges of today's threat landscape.
The adoption of the Zero Trust model offers several advantages over traditional perimeter-based security models, helping organisations to better protect their valuable digital assets and information. Key benefits of the Zero Trust model include:
As data protection regulations continue to evolve and become more stringent, organisations are under increasing pressure to demonstrate their commitment to safeguarding sensitive information. The Zero Trust model's emphasis on granular access control, continuous monitoring, and robust IAM solutions can help organisations meet compliance requirements and maintain the trust of their customers and stakeholders.
The Zero Trust model's flexible architecture allows organisations to adapt to new and emerging cyber threats more effectively. By continuously monitoring and analysing network activity, security teams can identify potential vulnerabilities and address them proactively. Moreover, the Zero Trust framework can be easily integrated with emerging security technologies, such as artificial intelligence and machine learning, to further enhance its threat detection and response capabilities.
While the initial implementation of the Zero Trust model may require investment in new technologies and processes, it can lead to long-term cost savings and improved operational efficiency. By eliminating the need for extensive perimeter defences and simplifying network management, organisations can reduce the complexity of their IT environment and focus on more strategic security initiatives.
In summary, the adoption of the Zero Trust cybersecurity model offers organisations a more comprehensive and adaptive security solution, better equipped to handle the challenges of modern threat landscapes and complex IT environments.
Despite its numerous benefits, the implementation of the Zero Trust model is not without its challenges. Organisations need to consider the following factors when planning to adopt this security framework:
Change can be difficult, particularly when it involves rethinking long-held beliefs and practices related to cybersecurity. Employees and stakeholders may be hesitant to embrace the Zero Trust model, especially if they are accustomed to traditional perimeter-based security measures. To overcome this resistance, organisations should invest in education and training to help employees understand the rationale behind the Zero Trust model and its benefits.
Implementing the Zero Trust model may require significant upfront investment in new technologies and processes. Organisations must allocate sufficient resources to ensure the successful integration of the Zero Trust model into their existing IT infrastructure. This may involve the acquisition of new hardware, software, and security tools, as well as the development of new policies and procedures.
The transition to a Zero Trust architecture can be complex, particularly for organisations with large, legacy IT environments. Integrating the Zero Trust model with existing systems and applications may necessitate reconfiguring network architectures, updating software, and redefining access controls. To minimize disruption and ensure a seamless transition, organisations should develop a detailed implementation plan that includes milestones, timelines, and contingency measures.
The success of the Zero Trust model relies heavily on the cooperation and vigilance of end users. As such, ongoing education and training are critical to ensure that employees understand their role in maintaining a secure environment. Organisations should develop comprehensive training programs that cover key topics such as proper password management, phishing awareness, and incident reporting procedures.
By acknowledging and addressing these challenges, organisations can mitigate potential risks and ensure a smoother implementation of the Zero Trust model, ultimately reaping its numerous benefits and strengthening their overall cybersecurity posture.
As technology continues to advance and cyber threats grow more sophisticated, the Zero Trust model is poised to play an increasingly significant role in shaping the future of cybersecurity. The following trends and developments highlight the growing importance of the Zero Trust approach:
As the limitations of traditional perimeter-based security models become more apparent, organisations are recognizing the need for a more comprehensive and adaptive security strategy. The Zero Trust model's ability to address complex IT environments and evolving threats make it a foundational approach for organisations seeking to improve their cybersecurity posture in the coming years.
The Zero Trust model's flexible architecture enables it to be easily integrated with emerging security technologies, further enhancing its effectiveness in detecting and responding to cyber threats. Some of these emerging technologies include:
As cyber threats become more complex and pervasive, it is increasingly important for organisations, security vendors, and governments to work together in developing and implementing effective cybersecurity strategies. The Zero Trust model promotes a collaborative approach to security by encouraging the sharing of threat intelligence, best practices, and technological advancements. This collaboration can help to foster a more secure and resilient digital ecosystem for all stakeholders.
In conclusion, the rise of the Zero Trust cybersecurity model reflects a broader shift in the way organisations approach security in the face of rapidly evolving cyber threats. By adopting and adapting the principles of Zero Trust, organisations can build a more robust and flexible security infrastructure capable of withstanding the challenges of the digital age. As the future of cybersecurity unfolds, the Zero Trust model is poised to play a central role in shaping the strategies and technologies that will define the next generation of digital protection.
The rise of the Zero Trust cybersecurity model represents a paradigm shift in the way organisations approach security, moving away from the traditional perimeter-based defences to a more holistic, adaptive, and comprehensive framework. As the digital landscape becomes increasingly complex and the sophistication of cyber threats continues to grow, it has become evident that traditional security models are no longer sufficient in providing the level of protection organisations require.
By embracing the key principles and components of the Zero Trust model, organisations can better defend against both external and insider threats, minimise the potential damage caused by security breaches, and maintain compliance with evolving data protection regulations. Furthermore, the flexibility and adaptability of the Zero Trust model ensure that it can be integrated with emerging security technologies and practices, helping organisations stay ahead of the ever-changing threat landscape.
As organisations continue to face new and evolving cyber challenges, the adoption of the Zero Trust approach offers a progressive and effective means of enhancing their cybersecurity posture. With its potential to reshape the cybersecurity landscape, organisations should seriously consider the Zero Trust model as an integral part of their comprehensive security strategy.
If you require assistance protecting your business this year, get in touch with our cyber security experts today and we'll help build a plan that protects your organisation.